“As a SaaS solution for risk management, you need to set a good example”
- Case Study

Perium is a leading online platform for information security and privacy risk management. It’s a company that knows very well that confidential information must remain well protected. The solution that Perium offers to customers is so versatile that, in addition to information security and privacy, it can also be applied to strategic and operational risk management. As a SaaS product, Perium can greatly reduce costs for the end user (such as consultancy hours).
Perium target customers are companies that are intrinsically exposed to risks surrounding privacy and information security. To ensure the security of their own platform, Perium enlisted the services of Hacksclusive.
Strong need for framed pentests
Perium approached Hacksclusive with a view to targeted and limited pentests. The basis of the platform already existed, and during development several questions arose about the security of a number of elements. "Because my partner, and co-founder of Perium, Jasper de Vries already has the necessary experience with pentesting, we were able to indicate where our needs lay. Hacksclusive was therefore able to test very purposefully," says Arjan.
It's easy to imagine that pentests are urgently needed in an organization that identifies security risks. Especially when it comes to a product in a cloud environment. Qualitative pentests in which thorough testing is carried out and findings are quickly translated into solutions is therefore very important.
Perium eventually came to Hacksclusive as a pentest partner. Arjan and Jasper had two reasons for this:
-
Hacksclusive has a good track record. Martijn Baalman is an internationally renowned pentester with a strong reputation.
-
Communication for Perium was particularly important. It was possible for Hacksclusive to communicate instantly with Perium and their soft devs. No fluffy reports - just straight to the point with interim findings.

Online environment instead of fuzzy PDFs
What particularly appeals to Perium about Hacksclusive's approach is the use of an online environment. The dashboard explains precisely what has been tested and what the findings are. A chat function enables immediate communication between the client and the ethical hacker who performs the pentests. This contrasts with many companies where you only receive a full report after a number of weeks have already passed.
The added value of Hacksclusive for Perium was primarily a result of the speed of the process. "I don't want to wait two weeks for a report if a critical error has been found - I want to know immediately, so that we can act on it quickly."
“The biggest compliment I can give to Hacksclusive is that I can't think of anything they could do better'.
Arjan Kremer, Founder Perium
.png?width=300&height=300&name=Ontwerp%20zonder%20titel%20(12).png)
No red flags
“There were certainly some surprising results from the pentests, otherwise we would have been able to find and fix it ourselves in advance,” says Arjan. “It is especially important that at the start of the pentest process we discussed what requirements our platform must meet, a list of security specifications based on the OAS (openAPI Specification) and OWASP (Open Web Application Security Project). If a finding is non-critical, then it is not an immediate priority. Fortunately, there were few red flags from the test, a nice confirmation that we are on the right track.”
"Pentesting has yielded many benefits for Perium. We can now present ourselves as being even more secure. We have a platform that makes the world a bit safer, so you must set a good example yourself. We do that with our ISO27001 certification and now also with pentesting".
Not 'done' after first results
Arjan is aware that pentesting is an ongoing process. "You're not done after you've received the results. We act on any findings that have been found and these must be retested by Hacksclusive. In addition, we must continue to test and validate, and continue doing this with every software update". If it's up to Arjan, there will be a role for Hacksclusive in this ongoing pentest proces.
Related stories
-
 blog posts
blog postsWhere do hackers come from?
Read moreAt Hacksclusive,every day our hackers help organisations make their digital products and services a little more secure. Our hackers do this by, for example, assessing the configuration of a Docker container or Kubernetes cluster, examining the source code of a REST API for possible vulnerabilities or testing the security of an Android app. Hacksclusive provides the knowledge and skills of its hackers as a service. The Hacksclusive platform plays an important role in this. It ensures that our hackers can work efficiently and have as much time as possible to discover vulnerabilities. Just as importantly, it not only gives our clients insight into which hacker did what, how, and when, but it also provides an understanding of the root causes of vulnerabilities and how the security of their digital products and services can be improved.
Of course, having such a platform sounds great. But without hackers, it’s worth nothing. So, where do hackers come from?
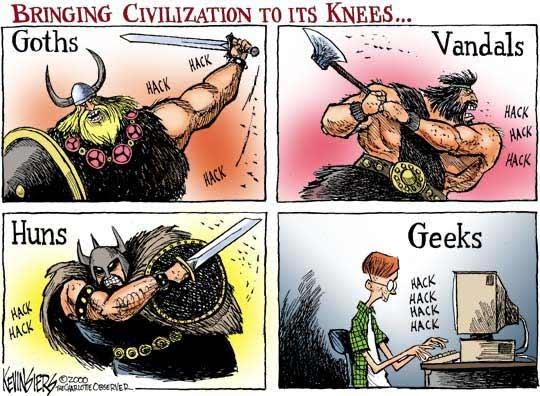
Origin of hacking
The word hacking is derived from the Germanic word hakkon and it literally means to chop. It wasn't until the 1980s that the word took on the meaning of “breaking into a computer”. The association of the word hack with the computer originated at the Massachusetts Institute of Technology (MIT) in the 1960s. Students in the model railroad club called any new connection or improvement to the train circuit a hack. Not much later, creative applications developed by scientists and students for the university computer—beyond the device's intended purpose—were also called “hacks.” The people who created them called themselves hackers.
-
 blog posts
blog postsCISO's are NPC's
Read moreOn Wednesday, October 9, the Platform for Information Security (PvIB), ISACA Netherlands Chapter, and NOREA, the professional organisation for IT auditors, organised the 20th edition of the Security Congress. Together with Edo Roos Lindgreen, I was one of the speakers. With the theme ‘Expect the Unexpected,’ I addressed, among other topics, the role of the CISO.
-
 blog posts
blog postsNavigating NIS2: a guide to cybersecurity compliance
Read moreAs of October 2024, NIS2 is legally mandatory, and to aid in preparation, the National Cyber Security Center has launched a self-evaluation tool. Organizations completing the self-evaluation can determine if they fall under the NIS2 directive and whether they are considered "essential" or "important" according to this directive for the functioning of society and/or the economy. Failure to comply with this law can result in legal consequences and potential fines. Therefore, it is crucial to make timely preparations and ensure that your organization complies with the requirements of NIS2.